Challenge
Ensuring the security of your company's digital assets has become a paramount concern in today's technological landscape. Whether it's safeguarding classified documents, protecting financial resources, or securing personal identities, you face the constant challenge of preventing unauthorized access and manipulation. Additionally, operational security is crucial, encompassing protection against external intrusions and ensuring the continuous availability of online services. As you navigate these complexities, finding a robust solution that addresses your specific security needs becomes increasingly vital.
.webp?length=500&name=Image%20(1).webp)
Solution
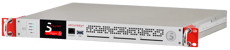
The Primus X-Series HSM offers top-tier security solutions tailored to your needs. It ensures swift and efficient operations up to 1000 RSA-4096 TPS (transactions per second). Its robust architecture enables storage of over 1 million keys across 120 partitions, each with a 240MB capacity.
Beyond key management, it handles authentication, encryption, and more, while allowing you to set up clusters yourself, offering geo-redundancy and load balancing. Partitioning allows support for multiple applications simultaneously, providing a scalable and personalized security solution. With the Primus X-Series HSM, you will confidently navigate IT security challenges, knowing your digital assets are safeguarded according to your needs.
.webp?length=200&name=Image%20(1).webp)
Key Benefits







True Random Numbers Generation (TRNG
High-entropy encryption keys are paramount to provide the highest security. The Primus X-Series HSM has multiple true random number generation (TRNG) modules. They are built up with separate hardware components and get their randomness from different physical noise mechanisms.
Crypto-Agile Architecture
Due to its dynamic architecture, the Primus HSM is quantum computer ready. Should quantum computers make any of the supported algorithms to become obsolete, then a quantum computer safe algorithm may be installed through a firmware upgrade.
API Integration and built-in security
Primus HSM provides a variety of APIs for secure integration and communication, supporting automatic failover, load balancing, and prioritization. High availability and clustering are built-in features, requiring no extra software or cost.
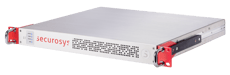
Swiss Made
Crafted entirely in Switzerland, Securosys Primus HSMs embody unmatched quality and reliability. Free from external influences, our Swiss-made HSMs guarantee the highest standards from development to production, ensuring unparalleled security solutions.
Use Cases
 Public Key Infrastructure (PKI) and Key Management System (KMS) Environments
The Primus X-Series HSM provides secure key generation, storage, and management, ensuring the integrity and confidentiality of cryptographic keys essential for PKI and KMS environments.
Public Key Infrastructure (PKI) and Key Management System (KMS) Environments
The Primus X-Series HSM provides secure key generation, storage, and management, ensuring the integrity and confidentiality of cryptographic keys essential for PKI and KMS environments.
 Certificate Management
Safeguard the entire certificate lifecycle, from issuance to revocation, with the Primus X-Series HSM, ensuring trust and authenticity in digital communications.
Certificate Management
Safeguard the entire certificate lifecycle, from issuance to revocation, with the Primus X-Series HSM, ensuring trust and authenticity in digital communications.
 Protection of the Blockchain
Secure blockchain operations by leveraging the Primus X-Series HSM to protect private keys and ensure the authenticity of blockchain transactions.
Learn more
Protection of the Blockchain
Secure blockchain operations by leveraging the Primus X-Series HSM to protect private keys and ensure the authenticity of blockchain transactions.
Learn more
 Smart Metering
Enhance the security of smart metering systems by using the Primus X-Series HSM to securely store and manage cryptographic keys, ensuring the accuracy and integrity of metered data.
Learn more
Smart Metering
Enhance the security of smart metering systems by using the Primus X-Series HSM to securely store and manage cryptographic keys, ensuring the accuracy and integrity of metered data.
Learn more
 Crypto Operations
The Primus X-Series HSM offers secure key storage and management, critical for safeguarding crypto assets.
Crypto Operations
The Primus X-Series HSM offers secure key storage and management, critical for safeguarding crypto assets.
 Identity Access Management (IAM) and Privileged Access Management (PAM)
Ensure secure identity verification and access control by using the Primus X-Series HSM to manage cryptographic keys that protect sensitive user credentials and privileged access.
Identity Access Management (IAM) and Privileged Access Management (PAM)
Ensure secure identity verification and access control by using the Primus X-Series HSM to manage cryptographic keys that protect sensitive user credentials and privileged access.
 Cloud Access Protection (Microsoft BYOK, AWS XKS, Salesforce, CASB, etc.)
The Primus X-Series HSM enables secure cloud operations by managing keys used in Bring Your Own Key (BYOK) scenarios, external key stores, and other cloud-based encryption services.
Cloud Access Protection (Microsoft BYOK, AWS XKS, Salesforce, CASB, etc.)
The Primus X-Series HSM enables secure cloud operations by managing keys used in Bring Your Own Key (BYOK) scenarios, external key stores, and other cloud-based encryption services.
 Docker Signing, Code Signing, Document Signing
Maintain the integrity and authenticity of software and documents with the Primus X-Series HSM, which securely manages the cryptographic keys used in signing processes.
Docker Signing, Code Signing, Document Signing
Maintain the integrity and authenticity of software and documents with the Primus X-Series HSM, which securely manages the cryptographic keys used in signing processes.
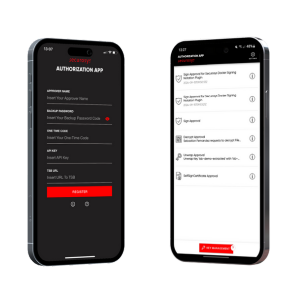
 eIDAS, ZertES, or QSCD Operations
Comply with European and Swiss digital signature regulations by using the Primus X-Series HSM to securely manage Qualified Signature Creation Devices (QSCD) for eIDAS and ZertES operations.
eIDAS, ZertES, or QSCD Operations
Comply with European and Swiss digital signature regulations by using the Primus X-Series HSM to securely manage Qualified Signature Creation Devices (QSCD) for eIDAS and ZertES operations.
 Database Security
Protect sensitive data within databases by using the Primus X-Series HSM to manage encryption keys, ensuring data remains secure both at rest and in transit.
Database Security
Protect sensitive data within databases by using the Primus X-Series HSM to manage encryption keys, ensuring data remains secure both at rest and in transit.
Technical Specifications
- Multi-barrier software and hardware architecture with supervision mechanism
Authentication (extract)
- 128/192/256-Bit AES with GCM-, CTR-, ECB-, CBC-, MAC Mode
- Camellia, 3DES (legacy), ChaCha20-Poly1305, ECIES
- RSA 1024-8192, DSA 1024-8192
- ECDSA 224-521, GF(P) arbitrary curves (NIST, Brainpool,...)
- ED25519, Curve25519, Ed448, BIP-0340, BIP-0341, SLIP-10
- Diffie-Hellman 1024, 2048, 4096, ECDH, X448
- SHA-2/SHA-3 (224 - 512), SHA-1, RIPEMD-160, SHAKE
- HMAC, CMAC, GMAC, Poly 1305
- Post-Quantum Cryptography (PQC) algorithms (optional)
ML-DSA, SLH-DSA, ML-KEM, HSS-LMS, XMSS
- Two hardware true random number generators (TNRG)
- NIST SP800-90 compatible random number generator
- Key capacity: up to 30 GB
- Up to 120 partitions @ 240 MB secure storage
- Number of client connections not restricted
- Unlimited number of backups, automated backup
- Several sensors to detect unauthorized access
- Active destruction of key material and sensitive data on tamper
- Transport and multi-year storage tamper protection by digital seal
- Cryptographic evidence of audit relevant parameters (keys, configuration, hardware, states, logs, time-stamping)
- Multiple security officers (m out of n)
- Identification based on smart card and PIN
- JCE/JCA provider
- PKCS#11 provider and OpenSSLv3 provider
- Microsoft CNG/KSP
- REST (TSB module)
- IPv4/IPv6
- Interface bonding (LACP or active/backup)
- Active clustering of multiple units for load-balancing and fail-over
- Monitoring and log streaming (SNMPv3, syslog/TLS)
- Local configuration (GUI, console)
- Remote administration (Decanus Terminal and SSH )
- Local and remote firmware update
- Network attached storage data transfer (WebDAV option)
- Secure log and audit
- Enhanced diagnostic functions
(transactions per second)
| Model | RSA 4096 |
ECC 256 |
ECC 521 |
AES 256 |
| X1000 | 1000 | 3000 | 550 | 5000 |
| X400 | 400 | 3000 | 550 | 2000 |
- Power supply:
- 100 ... 240 V AC, 50 ... 60 Hz
- 36 ... 75 V DC
- Power dissipation: 60 W (typ), 80 W (max)
- Ultra capacitors for data retention
- Backup lithium battery: Lithium Thionyl Chloride 0.65g Li, IEC 60086-4, UL 1642, 3.6V
- 4 Ethernet RJ-45 ports with 1 Gbit/s (rear) 1
- RS-232 management port (front)
- 1 USB management port (front)
- 3 Smart card slots
- 3 slots for Securosys Security smart cards
- 4 LEDs for system and interface status (multicolor)
- 1 liquid crystal display for management information
- Console interface (local, SSH)
- Optional Decanus Terminal for remote administration
- EMV/EMC: EN 55022, EN 55024, FCC Part 15 Class B
- Safety: IEC 62368-1
- Temperature ranges (IEC 60068-2-1 Ad, IEC 60068-2-2 Bd): storage -25 ... +70 °C; operation 0 ... +40 °C,
recommended 1 ... +30 °C - Humidity (IEC 60068-2-78 Cab): 40 °C, 93% RH, non-condensing
- MTBF at tamb=25 °C: 100 000 h
- Dimensions (w×h×d) 440 x 88 x 441 mm
(2U 19" EIA standard rack) - Weight 13.5 kg
- Common Criteria EAL4+
- CC EN 419221-5 eIDAS protection profile
- CC EN 419241-2 Sole Control (SAM)
- FIPS
- FIPS140-2 Level 3
- FIPS140-3 Level 3 (in certification)
- CE, FCC, UL
Related Products
 Primus HSM Cyber Vault (X2 Models)
The Hardware Security Modules that combine performance and cyber security innovation
Primus HSM Cyber Vault (X2 Models)
The Hardware Security Modules that combine performance and cyber security innovation
 Primus HSM CyberVault Core
Next-Generation Cryptographic Protection at an Unmatched Performance/Price Ratio
Primus HSM CyberVault Core
Next-Generation Cryptographic Protection at an Unmatched Performance/Price Ratio
 Primus HSM E-Series
Enterprise level Hardware Security Module at an unbeatable performance/price ratio
Primus HSM E-Series
Enterprise level Hardware Security Module at an unbeatable performance/price ratio
 Decanus Terminal
Remote management device for your HSM and user partitions
Decanus Terminal
Remote management device for your HSM and user partitions