Smart Key Attributes (SKA)
Challenge
How can organizations enforce compliance and approval policies on cryptographic key usage?
Hardware Security Modules (HSM) are designed to ensure that private keys cannot be extracted. However, they do not fully control how keys are used once access is granted.
This creates a critical vulnerability: even with credential rotation and secure connections, a compromised or malicious application can misuse private keys without extracting them.
This risk is especially severe in blockchain and digital asset environments, where:
- Transactions are irreversible
- Counterparties are anonymous
- Misuse cannot be undone
As a result, organizations need strong, policy-based control over key usage, not just key storage, to meet security and compliance requirements.
Solution
Securosys Smart Key Attributes (SKA) are a patented technology that enables HSM-enforced policies defining how and when private keys can be used.
SKA allows organizations to attach fine-grained authorization rules directly to each key, such as:
- Multi-party approval (m-of-n quorum)
- Time-based restrictions (timelock, timeouts, expiration)
- Allowed cryptographic operations (e.g., sign, decrypt, unwrap)
Unlike traditional approaches, SKA ensures that authorization is enforced inside the HSM, not by the application. This means that even if an application is compromised, unauthorized key usage is prevented.
These policies benefit from the same tamper-resistant protection and physical security boundaries as the keys themselves and are covered by Common Criteria EAL4+ and FIPS 140-3 Level 3 certifications.
SKA is available on both Securosys Primus HSM (on-premises) and Securosys CloudHSM, and can be integrated via:
- Java (JCE) API
- PKCS#11 API
- REST API through the Transaction Security Broker (TSB)
Key Benefits



Highly Customizable Authorization Rules
SKA allows organizations to define granular, policy-driven controls per key, aligning security rules with business workflows and compliance requirements.
Enforcement Inside the HSM
By enforcing authorization within the HSM, SKA removes reliance on external application logic, significantly reducing the risk of misuse due to compromised systems.
Swiss-made
Designed, developed, and manufactured in Switzerland, Securosys solutions meet the highest standards for security, quality, and reliability.
Use Cases
 Digital Identity Protection
Digital Identity Protection
How does SKA protect digital identities?
SKA ensures that private keys used for identity, authentication, and certificates are only used under defined conditions, reducing the risk of unauthorized access and supporting regulatory compliance.
 Signature Services According to eIDAS
How does SKA support eIDAS-compliant signing?
Signature Services According to eIDAS
How does SKA support eIDAS-compliant signing?SKA enables end users to retain control over their signing keys while enforcing authorization policies required for Qualified Trust Service Providers (QTSPs), ensuring secure and legally recognized remote signatures.
 Banking & Fintech Transaction Security
How does SKA secure financial transactions?
Banking & Fintech Transaction Security
How does SKA secure financial transactions?SKA embeds compliance and approval rules directly into key usage, ensuring that transactions are executed only when predefined conditions are met, reducing fraud risk and strengthening trust in digital asset operations.
FAQ
What are Smart Key Attributes (SKA)?
SKA brings HSM-enforced authorization policies to private keys stored on Securosys HSMs. They allow organizations to define rules such as multi-party approval, time restrictions, and permitted cryptographic operations directly on each key.
How does multi-party authorization (m-of-n) work with SKA?
SKA allows organizations to define quorum-based approval rules, where a minimum number of authorized users (m) out of a group (n) must approve a key operation before it is executed.
Can SKA enforce time-based restrictions on key usage?
Yes. SKA supports timelocks, timeouts, and expiration times, ensuring that keys can only be used within defined time windows or under specific conditions.
How do Smart Key Attributes enhance the security architecture of HSM-based systems?
SKA improves HSM security by shifting authorization from the application layer to the secure boundary of the HSM. This ensures that even if an application is compromised, private keys cannot be misused without meeting predefined authorization conditions.
Is SKA compatible with blockchain and digital asset use cases?
Yes. SKA is particularly well-suited for blockchain environments, where transactions are irreversible. It enables secure multi-signature workflows and strict approval processes to prevent unauthorized transactions.
How can SKA be integrated into existing systems?
SKA can be integrated using:
- Java (JCE) API
- PKCS#11 API
- REST API via the Transaction Security Broker (TSB)
The TSB is the recommended approach, as it provides a built-in workflow engine and simplifies multi-party authorization management.
What certifications support SKA security?
SKA benefits from the same protection as Securosys HSMs, including Common Criteria EAL4+ and FIPS 140-2 Level 3 (140-3 in process) certifications, ensuring high assurance for secure key management and authorization enforcement.
Related Products
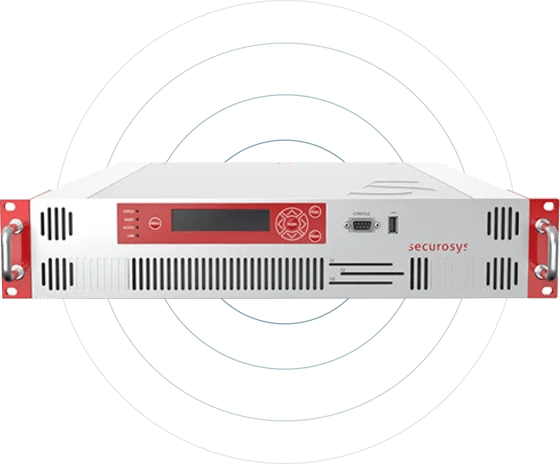
 Primus HSM Overview
Gain Full sovereignty over your data with Securosys Primus HSM, ensuring the utmost security standards
Primus HSM Overview
Gain Full sovereignty over your data with Securosys Primus HSM, ensuring the utmost security standards
 Primus Blockchain HSM
Enhancing blockchain security and crypto asset protection
Primus Blockchain HSM
Enhancing blockchain security and crypto asset protection
 Transaction Security Broker
Unique and simplified key-usage workflows for financial and digital asset applications
Transaction Security Broker
Unique and simplified key-usage workflows for financial and digital asset applications
 CloudHSM
CloudHSM provides a seamless, secure, and cost-effective path to achieving full compliance with data security requirements and regulations
CloudHSM
CloudHSM provides a seamless, secure, and cost-effective path to achieving full compliance with data security requirements and regulations